
EDR, MDR, and XDR Comparison: The Key Differences Explained

Cyber threats are no longer simple viruses that traditional antivirus tools can easily detect. Instead of being opportunistic, threat actors are now highly skilled, organised, and patient. They will use deceptive strategies like fileless malware, stolen credentials, social engineering, and multi-stage attacks to help bypass security tools.
The reality of an evolving threat landscape has made advanced endpoint security tools an essential investment no matter if you’re a global enterprise or an SME. The fallout from a cyberattack can have devastating consequences that can bring operations to a standstill, damage customer relationships, and lead to regulatory fines.
Did You Know?

88% of ransomware attacks happen outside of normal business hours*

40% of organisations hit by a ransomware attack say lack of cyber security expertise contributed to an attack*

$1.53 million – is the average cost to recover from a ransomware attack, that’s even before paying a ransomware payment*
If you’ve been weighing up your options for improving your business’s security posture, you may have come across terms like EDR, MDR, and XDR in discussions with your Managed Service Provider (MSP).
EDR, MDR, and XDR all sound alike, but in reality, they are very different solutions. If you are looking to invest in these services, it’s important to understand what sets them apart so you can have the right balance of security, cost, and operational skills.
In our latest blog, we explore the key differences between EDR, MDR, and XDR, along with which solution can offer the best protection today and has the resilience needed for the future.
EDR, MDR, and XDR Comparison: Which One is Right For You?
- EDR - Endpoint detection and response
- MDR - EDR plus 24/7 expert monitoring and response
- XDR - All the above, including automation that stops ransomware and provides broader visibility across endpoints, email, identity, cloud, etc.
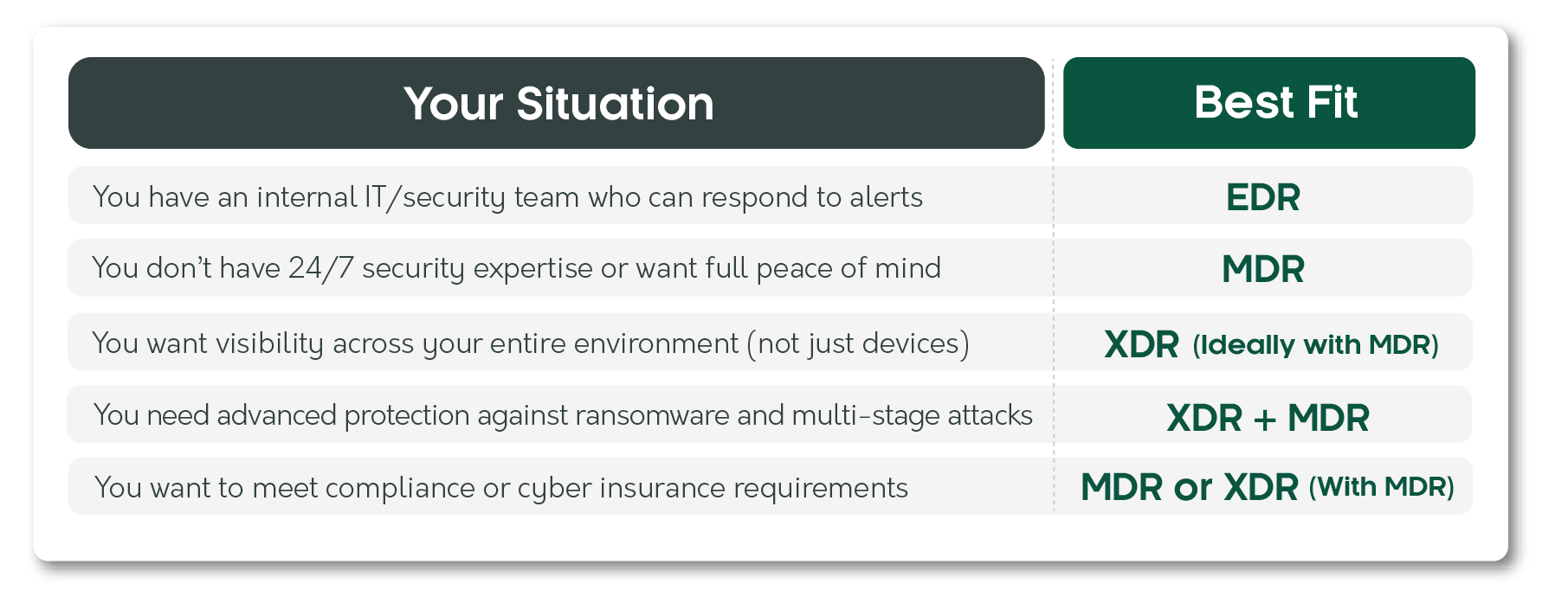
It's important to note that XDR gives broader visibility, but it isn’t the same as a managed 24/7 response service unless paired with MDR.
What is Endpoint Detection and Response (EDR)?
Endpoint Detection and Response, also known as EDR, is a tool that is installed on endpoints like laptops, desktops, servers, and mobile devices. EDR continuously monitors these endpoints for malicious activity, helping to stop threats before they can spread throughout your IT systems, causing costly operational downtime.
EDR provides real-time visibility into suspicious activity, and it will alert your team immediately when a threat is detected. Your team can then analyse incident data to discover what has happened and its effects and respond to the incident using in-built investigation tools. EDR also automates responses such as isolating compromised endpoints, stopping threats, blocking attacker access, and reducing dwell time.
What Does an EDR Service Give You?
- Advanced threat detection on endpoints
- Real-time monitoring and alerts
- Detailed threat investigation tools
What is the Best Application for EDR?
EDR is an excellent baseline endpoint security solution that provides deep visibility at device level. It’s effective at detecting advanced threats before they can cause devastating damage. EDR is best suited to businesses with an existing internal or external security team, as it requires the expertise to monitor alerts and respond to threats in real time. If your business is at the start of building its own cyber security strategy, EDR will give you a solid foundation for future scalability to MDR or XDR.
What is Managed Detection and Response (MDR)?
Managed Detection and Response, or MDR, combines the benefits of EDR with human expertise to oversee and secure your systems 24/7. MDR is a service-led approach that integrates monitoring, investigation, threat hunting, and cyber incident response. When your provider is notified about an incident, expert security analysts who understand modern threats will investigate and resolve the issue. Remediation actions can include isolating endpoints, deactivating accounts, or supporting your internal team to fix the issue so the threat does not spread further. By deploying MDR, threats are often contained with minimal disruption before a business has even become aware of the issue.
What Does an MDR Service Give You?
- Advanced threat detection on endpoints
- Real-time monitoring and alerts
- Detailed threat investigation tools
- 24/7 security expert monitoring
- Proactive threat hunting
- Expert response
What is the Best Application for MDR?
Many SMEs lack 24/7 expert threat detection and response to proactively neutralise incidents. MDR fills this gap for organisations without an internal IT security team or for those operating outside of standard business hours. It’s also an ideal solution for businesses that must meet compliance requirements or want to lower their cyber insurance premiums.
What is Extended Detection and Response (XDR)?
Extended Detection and Response, also known as XDR, expands protection beyond endpoints like computers and servers. It delivers unified prevention, protection, detection, and response across email, identity, cloud applications, and infrastructure.
Modern threats often start with a phishing email, move to a cloud account, and ultimately spread to devices. If your security tools work separately, these events can appear to be unrelated incidents. XDR gives a holistic attack view, making the connection between these different occurrences while filtering out false alarms.
By correlating data from multiple sources, XDR will detect multi-stage attacks that can go undetected if viewed independently. By streamlining attack investigation using AI, teams can act quickly to prevent sophisticated threats from spreading across your digital ecosystem. This helps prevent costly downtime and reputational damage, along with reducing the chance of the same attack unfolding again.
What Does an XDR Service Give You?
- Advanced threat detection on endpoints
- Real-time monitoring and alerts
- Detailed threat investigation tools
- 24/7 security expert monitoring
- Proactive threat hunting
- Expert response
- Email security monitoring
- Microsoft 365 protection
- Cloud application security
- Cross-platform threat protection
- Optional network traffic analytics
What is the Best Application for XDR?
For businesses that use cloud applications, cloud storage, remote workers or operate in a regulated industry, XDR provides deeper visibility across networks. It delivers advanced protection from modern threats that device-only monitoring might miss while improving threat correlation and reducing false alarms.
It is worth remembering that, like EDR, XDR is just a monitoring platform that improves the visibility of threats. XDR does not provide 24/7 human-led oversight unless it is paired with MDR.
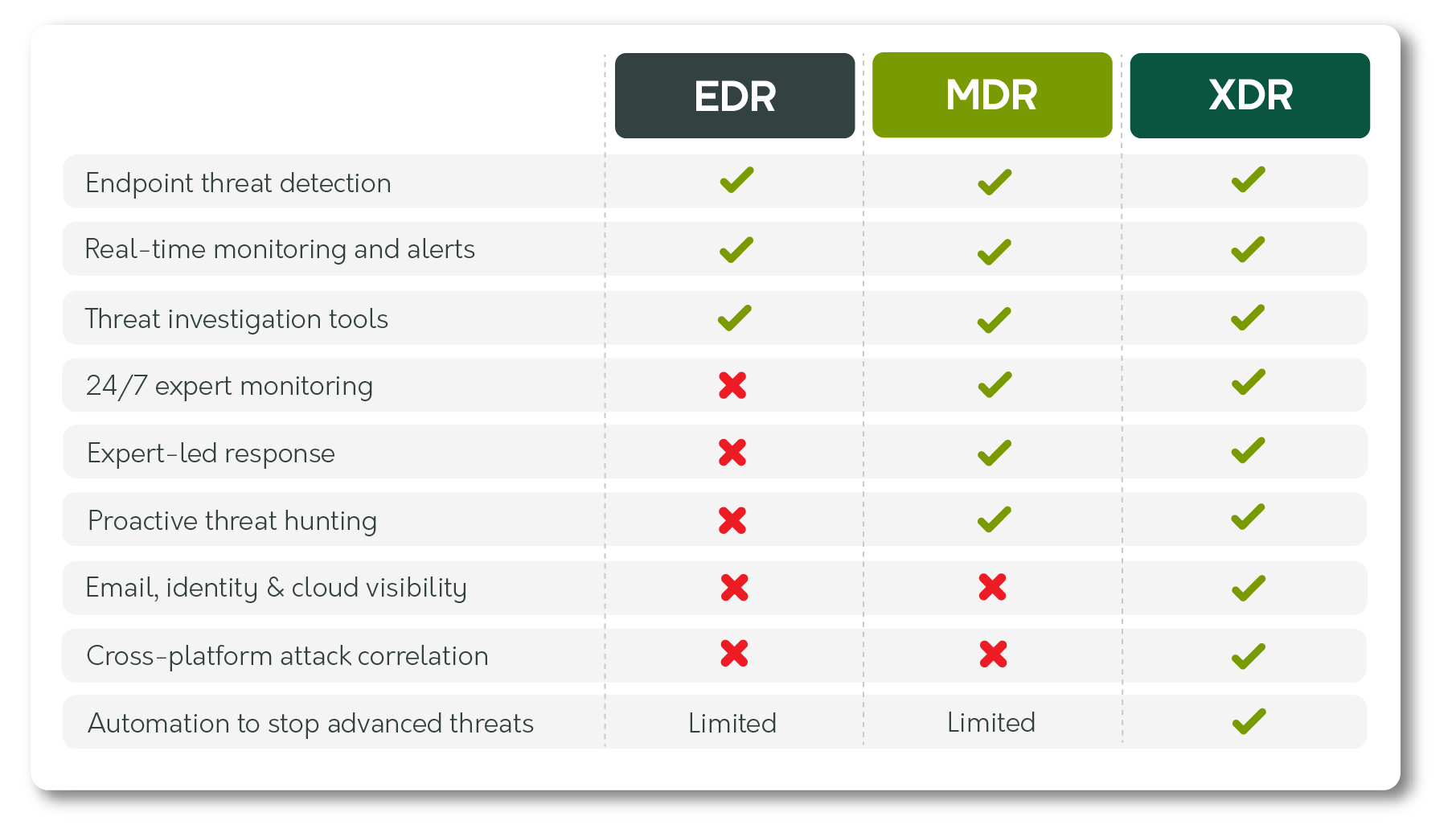
EDR, MDR, and XDR Comparison: What's Included?
The table below provides a side-by-side comparison of EDR, MDR, and XDR, showing the level of security that they each offer.
Choosing the Right Approach for Your Security Strategy
In our EDR, MDR, and XDR comparison, we've highlighted that they offer varying levels of visibility, protection, and expertise. EDR focuses on protecting individual endpoints. XDR extends this security across your wider digital environment. While MDR provides the peace of mind that experienced human professionals are monitoring and responding to threats in real time.
The level of security you choose will depend on a variety of individual factors, including your risk threshold, in-house skills, and operational needs.
Investing in building a robust cyber security strategy is ultimately about ensuring business continuity. Having the right detection and response capabilities in place will mean threats are quickly identified and contained, limiting the operational effects on your business.
By working with an MSP, like Croft, we can recommend the right level of detection and response by taking time to understand your individual requirements. We’ll also ensure you have a clear roadmap for deployment of your chosen solution. Our advanced EDR, MDR, and XDR protection is backed by responsive support, developed to provide complete confidence in an evolving threat landscape.
You can find out more about how Croft can secure your business against modern threats by viewing our Endpoint Security page, or you can contact one of our experts.
We are always happy to help and are here to answer any questions you might have.
Sources

Nikoo Fullerton
Nikoo has 16 years of experience in tech, including 8 in cyber security. He started in technical support, moved into security consulting, and later into Strategic Account Management, giving him insight into both technical and business challenges. He works with organisations to improve culture through a framework that aligns people, processes, and technology, with a focus on strong cyber hygiene and best practices. His approach is top-down, driving strategic, outcome-based solutions led by senior leadership and the board.